Sending Secure Email
State Employee Homepage
IN.gov sites now using HTTPS
Cybersecurity Awareness Training
Sending Secure Email
On April 22nd, IOT turned on Microsoft’s Data Loss Prevention 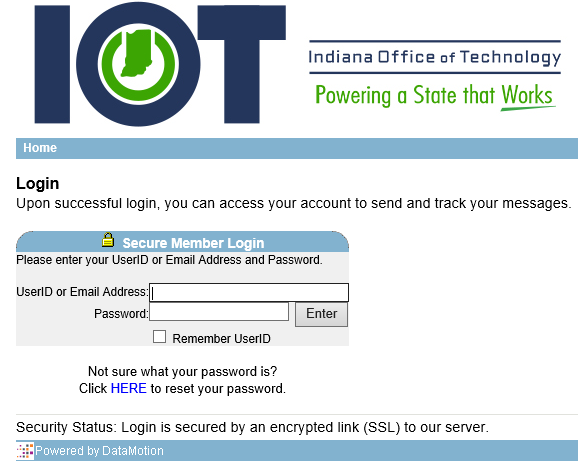 (DLP) capabilities for emails leaving the State network (to external addresses). This replaces another product that was blocking emails that contained over a thousand (1,000) instances of Personally Identifiable Information (PII) (e.g., SSN, Credit Card). Now, all emails that contain instances of PII will be blocked if the user doesn’t use “$ecure” in the subject line, or send via the https://certifiedmail.in.gov portal.
(DLP) capabilities for emails leaving the State network (to external addresses). This replaces another product that was blocking emails that contained over a thousand (1,000) instances of Personally Identifiable Information (PII) (e.g., SSN, Credit Card). Now, all emails that contain instances of PII will be blocked if the user doesn’t use “$ecure” in the subject line, or send via the https://certifiedmail.in.gov portal.
If a user attempts to send PII externally without sending via secure email (using either of those two options), an email will be sent to the user indicating that the message wasn’t sent, and in order to properly send it, they need to use secure email. Since implementing this change, more than 800 messages have been blocked.
IOT made this change to help prevent the accidental leaking of citizen PII.
If a user hasn’t sent a message with secure mail previously, an account will be automatically created if they send a message to an external address using “$ecure” in the subject line.
For more information and instructions about secure email, go to https://www.in.gov/iot/2745.htm and look at the bottom three FAQs.
State Employee Homepage
Working with the State Personnel Department, IN.gov this week launched a new version of the IN.gov homepage specifically for state employees. Visit IN.gov while connected to the state network and you will automatically be sent to this page.
If you prefer to go to the public version of IN.gov, you can do this by clicking Public Homepage (highlighted in the red box), or change the preference entirely in Site Settings and always go to the public homepage..
The site includes frequently visited links, including to Peoplesoft and Self-Service Password Management. SPD will be changing the top banner items on a regular basis to let employees know about important information and programs.

IN.gov sites now using HTTPS
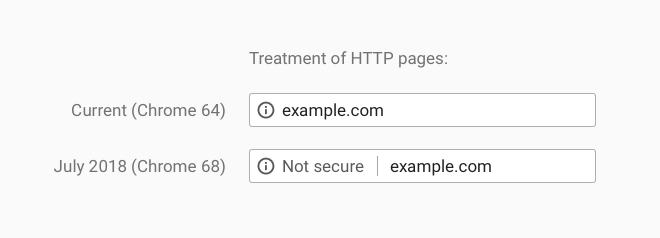
Starting in July, Chrome web browsers will begin alerting users that websites not using HTTPS:// are “not secure”. The 'S' at the end stands for 'Secure'. To prepare for this change, and for when other browsers follow suit, the Office of Technology implemented a change requiring the use of the HTTPS protocol for all access to www.IN.gov. Any attempts by users to access via standard HTTP will be automatically redirected to HTTPS.
Secure web pages have either a Green Lock icon or Green Address bar to indicate the sites are secure.
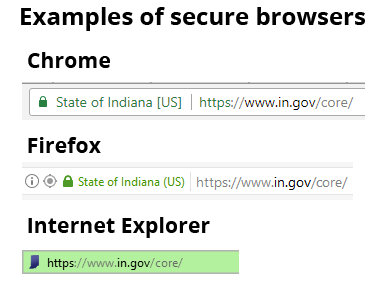
If the visitor happens to type http://www.IN.gov, they sent to https://www.IN.gov automatically. The same applies to any agency pages.
If a page is not labeled as secure, visitors will still be able to access the page.
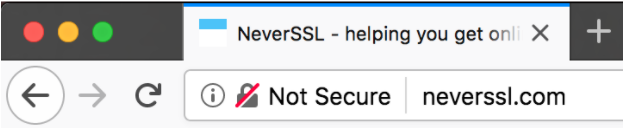
What will the browser look like if the page is not secure?
Here are examples of the Chrome (first image) and Firefox (second image) warning messages for pages that are not secure.
What does this mean when I am editing my website?
- Within the HTML
- If you have access to edit HTML from within WebCMS, stop using any reference to ‘http://’ in your images, iframes, css, javascript, or other references.
- You are safe to replace with ‘https://’
- You can also use a relative reference by just starting with ‘//’
- Anything with ‘src=’ should be changed
- All items within the content management system asset manager will be converted automatically and require no changes.
- You do NOT need to change all of your links (anchor tags, <a>).
- These can remain HTTP, as the redirect will automatically happen
- It is advised that moving forward you use ‘https://’ or a relative reference ‘//’
- If you have access to edit HTML from within WebCMS, stop using any reference to ‘http://’ in your images, iframes, css, javascript, or other references.
- Check for the green lock in the browser URL bar to confirm your static pages are secure
- If you do not see the green lock…
- Confirm you are testing using ‘https://’ first
- Consult browser developer console to find the reference error
- If you do not see the green lock…
- Note: the portal, https://www.in.gov/ will support TLS 1.1 and 1.2.
My page is showing up as unsecure, what should I do?
First, users can still get to the web page. The most likely cause is that there is a picture or other embedded item that is linked to that a site outside of IN.gov. If any one item on a page is HTTP://, then the entire page gets marked as Not Secure.
If you notice any www.IN.gov/ pages listed as 'Not Secure,' please submit a ticket at http://www.in.gov/inwp/2437.htm and the IN.gov team will assist.
Cybersecurity Awareness Training
IOT this week kicked off a new cybersecurity training for state employees. Though we have many layers of protection in place for a multitude of threats it is commonly understood that humans are the weakest link in cyber defenses. This program is designed to raise awareness and help our workforce ward off the threats and circumstances that could lead to a security breach.
IOT has set a target for agencies to reach a 90% completion level for each module.
On the first day, more than 4,000 users completed the training. Some notes to be aware of as the rest of employees complete the first training module.
- Some users with Internet Explorer as their browser are seeing the awareness module window open with the browser sized too small. Pressing the F11 key solves the issue, enlarging the screen to full size. Chrome and Firefox browsers do not have this problem.
- We’ve also had some experience the age old training problem, the pop-up blocker is on and the training window cannot open.
To access the Indiana Cyber Security Awareness Training, please log into PeopleSoft ELM and visit your "My Learning" page.
If, after clicking the above link, you need directions on how to log into PeopleSoft ELM, please visit https://www.in.gov/spd/2367.htm.
Register for self-service password management today and you won't need to call the IOT Customer Contact Center to reset your password!
Go to https://password.IN.gov
